According to the latest rumors, both Evasi0n and Pangu jailbreak utilities have been recently nominated for 2014 Pwnie Awards. This award is presented to those developers and security researchers, who find bugs or important exploits in the software. This year’s award will be given to a developer (or the developers) that made some important discoveries in the period of the past twelve months.
Both the Evasi0n and Pangu jailbreaks for iOS 7 have been nominated for 2014 Pwnie awards. The Pwnie Awards celebrate the achievements of security researchers and developers who find certain bugs and exploits. The awards cover bugs disclosed over the last year (July 2013 – June 2014).
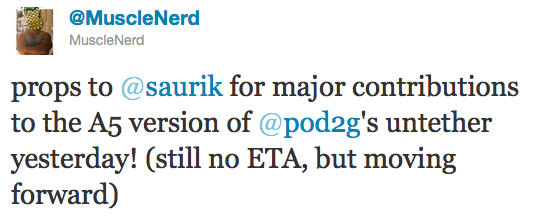
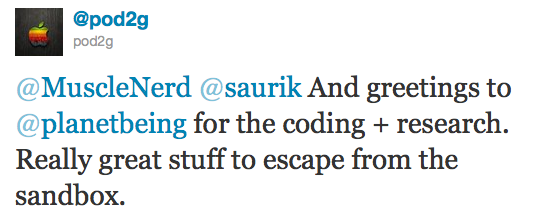
Last year the Pwnie Award was given to a developer nicknamed Planetbeing. It is very difficult to predict whom judges will choose this year as both Evasi0n and Pangu tools for jailbreak are worth winning the award.
If to speak about me, I would probably choose Evasi0n as the people behind this product were using their own exploits and methods for jailbreaking iOS 7, unlike the authors of Pangu.
[via ]