
Apple have recently released iOS 4.3.4 for , iPhone 3GS, iPad 1, iPad 2, iPod Touch 3G and iPod Touch 4G. Here are the direct links for each device that is supported by the update:

Apple have recently released iOS 4.3.4 for , iPhone 3GS, iPad 1, iPad 2, iPod Touch 3G and iPod Touch 4G. Here are the direct links for each device that is supported by the update:
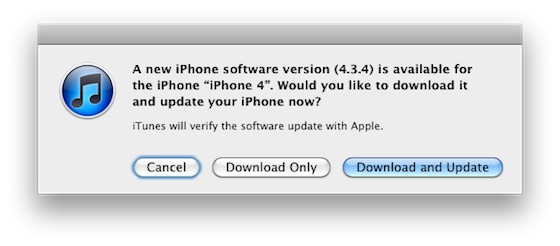
Apple has released iOS 4.3.4 to block the PDF exploit used by comex in JailbreakMe utility. JailbreakMe can wireless jailbreak all devices on iOS 4.3.3.
iOS 4.3.4 Software Update
Fixes security vulnerability associated with viewing malicious PDF files.Products compatible with this software update:
• (GSM model)
• iPhone 3GS
• iPad 2
• iPad
• iPod touch (4th generation)
• iPod touch (3rd generation)
For iPhone 4 Verizon Apple released iOS 4.2.9.
The official information is available here:
iH8Sn0w has released a new version of Sn0wBreeze 2.8 b4 with iOS 5.0 beta 3 jailbreak support. Sn0wBreeze is a so-called PwnageTool for Windows, an application that creates a custom ipsw with jailbreak preserving old baseband.
The jailbreak is tethered for , iPhone 3GS (new bootrom), iPad, iPod Touch 3G and iPod Touch 4G. Jailbreak is untethered for iPhone 3GS with old bootrom.
You can download Sn0wBreeze 2.8 b4 here.
sn0wbreeze v2.8 BETA 4 Release Notes:
--------------------------------------------- sn0wbreeze v2.8b4 -- For iOS 5.0 b3(9A5259f) --------------------------------------------- * Intended only for developers (as usual). * Hacktivation is disabled (again). * MAKE SURE YOU UPDATE TO iTunes 10.5 BETA 3! --------------------------------------------- Supported Devices/Tethered? --------------------------------------------- iPhone 3G[S] (old bootrom) [UNTETHERED] iPhone 3G[S] (new bootrom) [TETHERED] iPhone 4 (GSM) [TETHERED] iPhone 4 (CDMA) [TETHERED] iPod Touch 3G [TETHERED] iPod Touch 4 [TETHERED] iPad 1G [TETHERED] --------------------------------------------- Those wondering, the jailbreakme exploit cannot be integrated into applications such as PwnageTool/redsn0w/sn0wbreeze. --------------------------------------------- redsn0w seems to be having sandbox errors due to it using the old b1 kernel. I and many others have not seen any issues with sn0wbreeze related to AppStore apps. If you prefer to use redsn0w, I am sure @MuscleNerd is working on a fix. --------------------------------------------- Download --> http://is.gd/sb28b4 --------------------------------------------- // iH8sn0w
As you might know hacker Comex has found a new PDF vulnerability and released JailBreakMe tool that uses it. These were great news. The bad ones is that your iPhone and iPad and iPod Touch is at risk. Bad guys can use the same vulnerability to take control of your device and do whatever they want with it.
Apple will fix it in iOS 4.3.4 firmware some day. Fortunately Comex has already released a patch for his JailbreakMe 3.0 exploit to protect already jailbroken devices from any malicious use of the exploit.
The package called ‘PDF Patcher 2′ can be downloaded and installed from Cydia. To jailbreak please use our step-by-step instructions.
Today Comex has officially released the new web-based jailbreak for iOS 4.3.3. It supports all devices including iPad 2.
The jailbreak uses a PDF exploit similar to old JailbreakMe and does not require your device to be connected to the computer.
To jailbreak, navigate to on your iOS device after updating to iOS 4.3.3 (if you do not need unlock). We will be posting detailed instructions shortly.
Here is the list of devices and iOS versions that are supported:
Step by step JailbreakMe tutorials:
MuscleNerd has announced in Twitter that iOS 5 has been successfully jailbroken using old good LimeRa1n exploit. Cydia and SSH is working without any problems.
iOS5 jailbroken on ipt4g: http://is.gd/7GxIcK http://is.gd/BwPvfh via limera1n + tethered boot..not too many surprises

Cydia works fine too from quick testing (I installed SSH) http://is.gd/oADWEo
It is currently tethered, that means jailbreak is gone after reboot. Hopefully i0n1c will be able to port his untether to iOS 5. Anyway great news for all jailbreakers!

I0n1c has confirmed that his untethered jailbreak exploit is still working for iOS 4.3.2. This is good news for all jailbreakers.
Here are his recent tweets:
Apple has been nice. I just verified that the untether vulnerability is not fixed in iOS 4.3.2 – my Ipad 1 is running untethered jailbroken
Of course the public untether binaries will not work with iOS 4.3.2 – I have to generate new untether binaries with new dyld/kernel offsets
I won’t be able to create all the untether binaries before sunday, because I will be on planes, …
The dev-team cannot produce the untether binaries on their own, because they don’t have the source code to the untether exploit.
Well from what I hear lots of the problems people had with 4.3.1 (like wifi, 3g, …) are gone in 4.3.2
The new version of iOS 4.3.2 jailbreak tools RedSn0w and PwnageTool will be released by the iPhone Dev-Team quite soon.
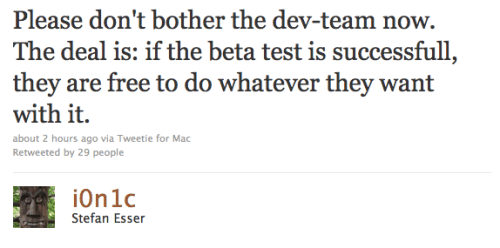
Hacker I0nic has given his untether exploit for the iOS 4.3.1 jailbreak to the iPhone Dev-Team. They will perform testing and integrate it into their jailbreak utilities – redsn0w and pwnagetool. This untethered jailbreak will probably work for iPhone 3GS, , iPod Touch 3G, iPod Touch 4G and iPad.
The iphone-dev-team is already beta-testing the untether. So it is up to them to give you your tool of choice.
Please don’t bother the dev-team now. The deal is: if the beta test is successfull, they are free to do whatever they want with it.
I0nic recently demonstrated his jailbreak on iPod Touch 4G. I hope to get iOS 4.3.1 jailbreak soon.
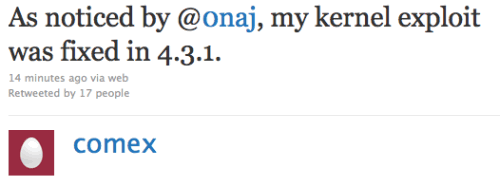
Comex, famous iPhone hacker, tweeted today that the kernel exploit for jailbreak he had found long ago was closed by Apple in recent iOS 4.3.1. This exploit could be used to jailbreak iPad 2.
As noticed by @0naj, my kernel exploit was fixed in 4.3.1.
I try not to be paranoid, but it is really hard to explain this as anything but a leak.
The funny thing is that my “new” kernel exploit is actually the kernel exploit used by JailbreakMe 2.0. It was never properly fixed.
It stayed there from 4.0.2 through 4.3, but was magically found in time for 4.3.1. well, go go @MuscleNerd and @i0n1c I guess
This is not good news. However we have recently seen working untethered jailbreak video. There are other vulnerabilities in iOS 4.3.1.
Here is a nice video for all jailbreakers. Hacker used sn0wbreeze to tether jailbreak iPod Touch 4G. Than he installed new untether exploit using SSH. Watch the result: